How to get llama 2 up and running , in a VM, with no GPU, and limited memory on Ubuntu
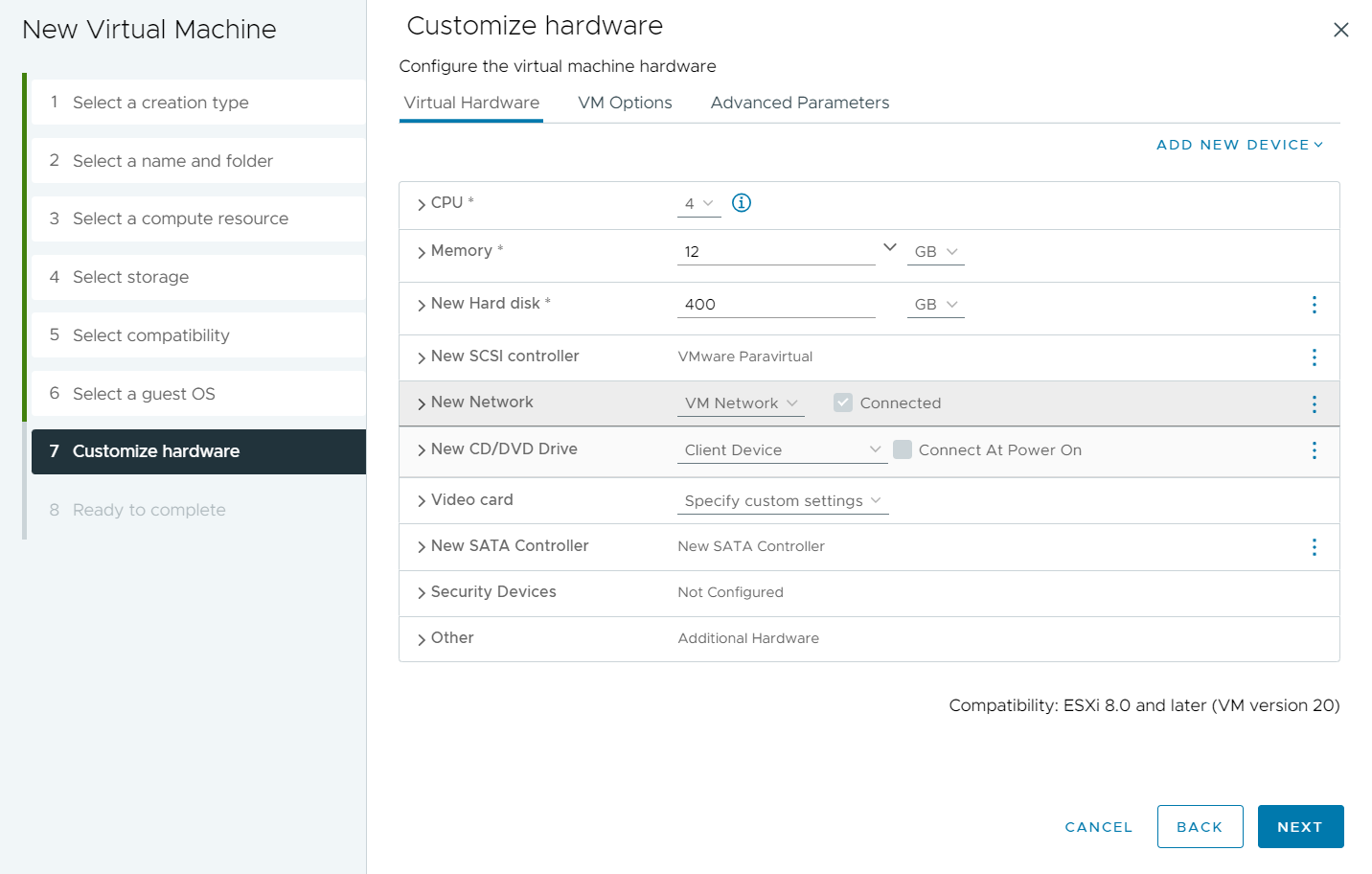
OK I decided to write this up after unsuccessfully being able to find all the required info I needed in one place. In this setup we will be using Ubuntu Server 22.04.2 LTS as the OS. I have this running on a home lab ESXi server 8, on a HP Compaq Pro 6300 SFF CPU = Intel Core i7-3770 Installed Memory 16 GB I have some 10K SAS drives installed for the VM's If you have not already, navigate to Get Ubuntu Server | Download | Ubuntu and download the 22.04.2 LTS ISO Next Lets create our VM that we are going to run this in. *Note Im using ESXi however you can probably do this in Workstation, Fusion, VirtualBox etc The main things to note on the VM creation. Set Ubuntu 64 bit as the guest OS Set your CPU relevant to the physicals CPU, I will be starting with 4 VCPU Set your Memory to as much as you can tolerate, I will be using 12 Disk Space - we are creating a 100G swap file, and the rest of the file can take up some room , so more is better if you can afford it Dont forget to add the U